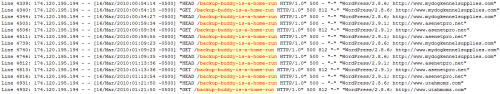
Now that I’ve weathered the storm and the attacks have subsided for now, I think it would be good to share with you what my raw access log files looked like during that day to see the distributed denial of service in action. Thanks to Kim Parsell, I was able to rename the raw access log file into a text file so I could examine it within NotePad++. Since a large amount of trackbacks were aimed at the backup buddy review I published, I performed a search in the log file for that post. Here is a sample of what I saw.
I’ve opted to use a screenshot instead of text as to not link to any of the sites within the log file. As you can see via the screenshot, the Backup Buddy post was being loaded every few minutes by one IP address. While I did receive a large number of trackbacks from a variety of websites, the log file clearly indicates that at least one IP address was the major culprit. It’s also interesting to note that this one IP address hosted different domains as you can see on the right. Those URLs on the right hand side were the ones generating the trackbacks. This makes me think that IP address is hosting a good sized splog network.
The two files that were blamed for sucking up resources on the shared server I was on, XMLRPC.php and Index.php are shown multiple times being accessed by a variety of IP addresses, not just the one shown in the first screenshot. This is where I think the attack was more distributed in nature.
What angers me is the fact that AnHosting, my original hosting provider of 3 years told me that they had an Automated Firewall System in place but because of the distributed nature of the attack coming from multiple IP addresses, they couldn’t tell what was legitimate traffic versus illegitimate. Their automated firewall must be broken because it should have blocked that IP address shown in the first screenshot.
None the less, I’m currently on HostGator now with WP-Super Cache installed. I just can’t help but think with a little more help from AnHosting, I wouldn’t have had to go through webhosting hell. But they operate on a three strikes rule with suspended sites. Once you hit the third strike, they do not lift the suspension of the site. Since I was on my second strike, I had to leave.

Always delete xmlrpc.php immediately from virtually all WP installs.
It’s responsible for several of the security issues with WP over the years, and it also allows unlimited password attempts. You can live without the mostly spam trackbacks for the safety of it being gone.
If you are on a dedicated or VPS (and you should be) I highly recommend the (free) configserver firewall http://configserver.com/cp/csf.html – it’s not just for cpanel anymore and it’s extremely good about blocking too many connections.
Last but not least when you can’t solve a ddos, replace apache with something like litespeed which is a drop in replacement (uses httpd.conf and .htaccess files directly unlike nginx). There is a free version and it can weather a ddos when apache would be long dead. Even automattic uses litespeed to this very day.