SiteLock, a website security company, has acquired Patchman, a Dutch security startup that offers automated vulnerability patching and malware removal for hosting providers. Prior to the acquisition SiteLock protected 6 million sites, with 2.2 million of them running on WordPress. The addition of Patchman extends SiteLock’s customer base to 12 million sites and more than 4 million of those are powered by WordPress.
Patchman detects vulnerabilities in a wide range of popular applications and quarantines and patches threats automatically. The quarantine feature neutralizes malicious files by removing them from public access. Patchman supports detection and patching for WordPress 3.x and later.
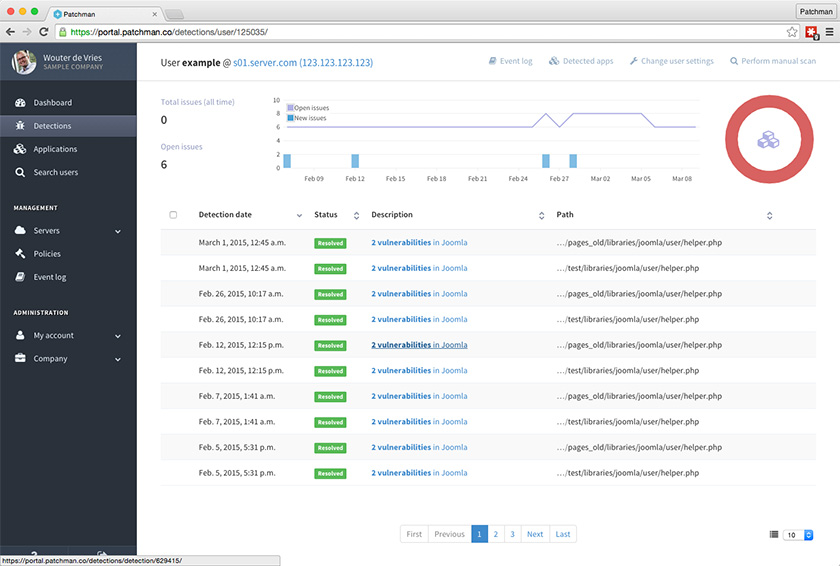
Historically, the service has not included patches for plugins but it has applied them on a case-by-case basis for high impact vulnerabilities, including a few found in WP Super Cache, MailPoet, and the open source Genericons font project. The Patchman dashboard allows users to easily track files where vulnerabilities have been detected, view status, and revert patches if necessary.
Patchman’s single focus on hosting providers gives SiteLock the opportunity to offer more options to its hosting partners. With the acquisition, the company is now partering with more than 500 hosting providers, including BlueHost, 1&1, Web.com, InMotion, Melbourne IT, GMO (NTT), and many others.
“During our early talks, Patchman was not looking to be acquired and SiteLock wasn’t looking to acquire,” SiteLock President Neill Feather said. After meeting at the WorldHostingDays show in Rust, Germany in late March this year and at another show in Los Angeles, the companies found they shared similar goals and would be in a better position working together.
“It truly was a matter of 1+1=3,” Feather said. “Traditionally, SiteLock is very strong in detecting and removing malware for end users. Patchman offers a service tailored specifically to hosting providers and aimed at fixing the security vulnerabilities that hackers exploit to infect websites with malware. By working together we are able to address a wider market and offer a broader solution to the problems that we solve for our customers. We can now attack the problem from multiple angles.”
Patchman’s technology will compliment SiteLock’s existing security features but the company has not yet decided how it will be incorporated into its security plans for customers. Feather said the team is still jointly building out its future roadmap to give hosts and end customers access to a wider range of products. They are also considering making Patchman’s detection technology compatible with more products in the WordPress ecosystem.
Feather could not disclose any specifics on revenue generated by SiteLock’s WordPress security products but approximately 30% of its newly expanded customer base is running on WordPress.
“What we can say is that we’re heavily invested in the WordPress community and plan on continuing to do so,” Feather said.
“I’m excited that the increased number of sites we now protect across multiple platforms means we’ll be able to identify malware and malicious trends more efficiently than we’ve been able to already, and that’s good for every end user,” SiteLock’s WordPress Evangelist Adam Warner said. “Secondly, although we already have solutions for our partners, Patchman allows web hosts to offer increased security options for advanced users of their platforms. Being a WordPress guy, I’m excited about the possibility we now have to extend the capabilities of Patchman to plugins and other WordPress-specific software.”

You make a big point of how many websites SiteLock is supposed to be protecting, but from what we have heard it sounds like a lot of their customers have been given some free SiteLock service, which they may not even be aware of, with their hosting account. It seems the purpose of that is so that SiteLock has a relationship with them that they can use to cold call them. Were you given any indication of how many of the websites they are supposed to be protecting are paying for the service and what kind of service they are getting, since a lot of their services don’t seem to offer much, if any, protection?
Also, websites running WordPress 3.7 or above would normally get security vulnerabilities in WordPress patched automatically without requiring any additional service due to the automatic background updates feature in WordPress.