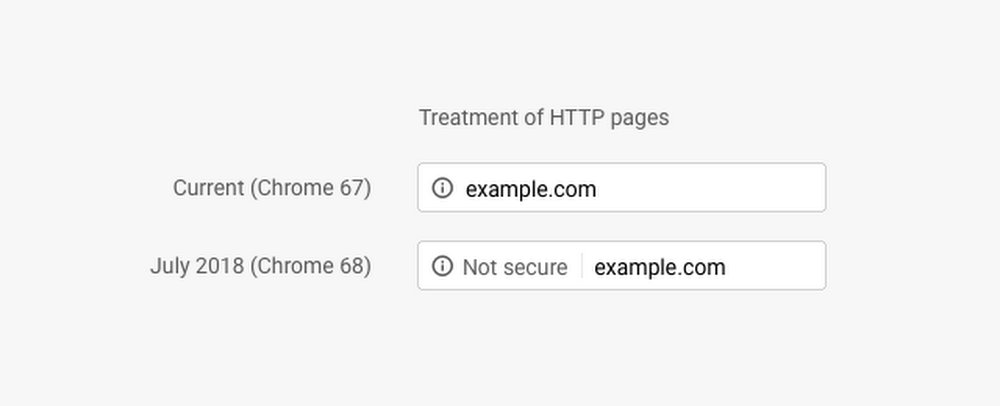
As part of a long term plan to push the web to adopt HTTPS encryption, Google Chrome is now marking all plain HTTP sites as “not secure,” as of July 24, 2018, with the release of Chrome 68. Previously, the “not secure” warning was hidden behind the security indicator in the URL bar as shown below.
That warning has become more prominent with the release of Chrome 68. The browser now immediately displays the “Not secure” message in the omnibox for all HTTP pages.
Today Google announced a time frame for eventually marking HTTP sites with a red “not secure” warning:
Eventually, our goal is to make it so that the only markings you see in Chrome are when a site is not secure, and the default unmarked state is secure. We will roll this out over time, starting by removing the “Secure” wording in September 2018. And in October 2018, we’ll start showing a red “not secure” warning when users enter data on HTTP pages.

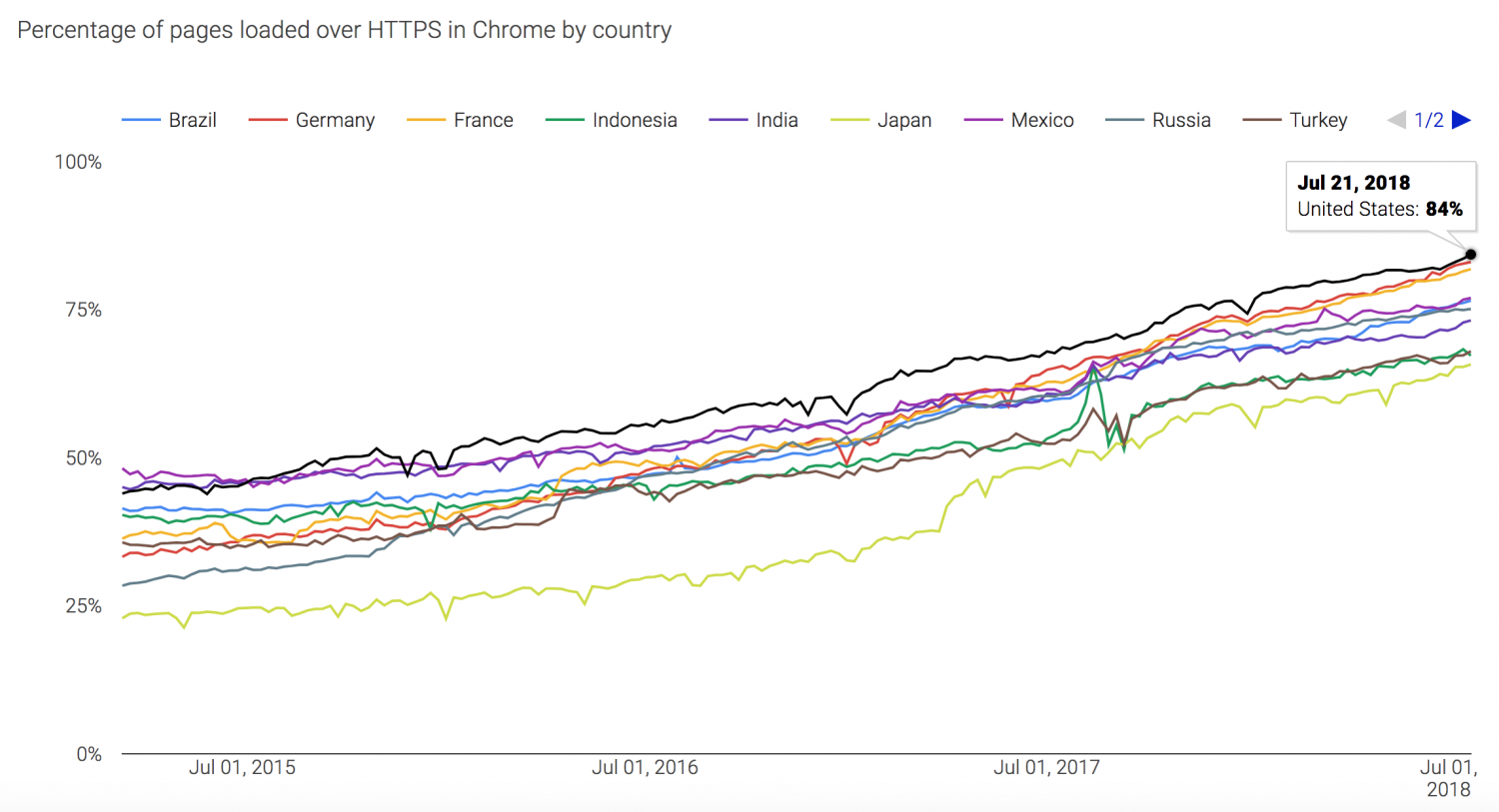
Google Chrome currently captures 60% of the browser marketshare worldwide, making it one of the company’s most effective vehicles for driving HTTPS adoption. Let’s Encrypt, the free and open certificate authority (of which Chrome is a platinum sponsor), has also been a key player in precipitating the rise in secure traffic over the past few years. Firefox Telemetry shows that HTTPS traffic is at 81% for US users and 73% for all users.
Google’s Transparency report shows similar numbers for percentage of pages loaded over HTTPS in Chrome. 84% of US traffic is encrypted by HTTPS.
Google has even more weapons in its arsenal for compelling website owners to switch to HTTPS. Even before Chrome began flagging unencrypted sites, the search engine added HTTPS as a ranking signal in 2014. It started as a lightweight signal that affected fewer than 1% of global queries. Google has also indicated that HTTPS may break ties between two equal search results, making a difference for competitive niches. With more sites adopting HTTPS as the norm, the company may choose to strengthen the signal in the future.
Not everyone is comfortable with a for-profit company making an aggressive push to require websites to deliver content over HTTPS. Some fear that prioritizing encryption in search results, while also using Chrome to cast doubt on websites’ security, is just the beginning.
Dave Winer, one of Google’s most vocal critics regarding this initiative, sees the push towards HTTPS as the company’s attempt to take control of the open web. His concern is that if Google succeeds, it might “make a lot of the web’s history inaccessible.”
“Google makes a popular browser and is a tech industry leader,” Winer said. “They can, they believe, encircle the web, and at first warn users as they access HTTP content. Very likely they will do more, requiring the user to consent to open a page, and then to block the pages outright.”
BTW, if I had to guess, the *real* reason Google hates HTTP has to do with Google's ad revenue, and not wanting Verizon and Comcast to remove their ads and replace them with their own. 😜
— Dave Winer (@davewiner) July 23, 2018
Others have speculated that another driving factor behind Google’s push for HTTPS adoption may be its investment in advancing PWA technologies, which require HTTPS to be enabled. Last year Google dumped Chrome apps from the Chrome Web Store in favor of building PWAs that can be installed on the desktop. HTTPS is a requirement for the permission workflows, new features, and updated APIs that the company is using to build its future products.
It’s easy to see how HTTPS is critical for e-commerce, banking, and other sites that collect highly sensitive data from users, but many wonder if it is necessary for simple blogs and content websites. Google contends that all websites need HTTPS protection to prevent intruders from injecting ads or exploits.
Few would dispute the value of HTTPS but critics are wary of Google establishing itself as the arbiter of safe browsing on the web.
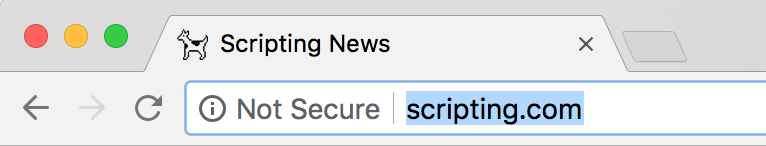
My blog, https://t.co/gPQ9VPYOLB, is not “not secure.” It uses the standard protocol of the web, HTTP. It will not hurt you.
— Dave Winer (@davewiner) July 24, 2018
For the moment, Winer seems to be committed to using HTTP to deliver his content. In Google’s feverish quest to push the entire web to adopt HTTPS, sites that are holding fast to HTTP on principle now appear as a sort of protest.
“This blog and all my other sites use HTTP,” Winer said. “I don’t see that changing. I expect this will make writing for the web more of a chore. That’s life I guess. I don’t want Google to be able to mold the web to its needs. I never signed on to being a Google developer, and never would. Basic rule: Google is a guest on the web, as we all are, and guests don’t make the rules.”


In regards to PWA, note that the previously-reported PWA feature plugin includes better support for HTTPS in WordPress as one of its purposes. This is because service workers depends on HTTPS to be installed.